Side-by-side, data loss and cyber-attacks are two of the most common concerns expressed by IT directors. Whilst ransom has traditionally been seen as a big cause of this, ransom (and subsequently) data loss appears to be changing. This blog explores an incident seen within a middle eastern financial customer from May-June 2022. This customer suffered large data loss and a high volume of files with a ransom note were written on its network, but the institution’s data was not encrypted. This is an example of a growing trend in ransomware attacks, which involves exfiltration of the victim’s data and the write of a ransom note but no encryption of files. Instead of being extorted for the decryption of their files, companies are being extorted for the return of their stolen data.
Attack Summary
A threat actor spread laterally through a customer network by writing suspicious ‘.dat’ and ‘.exe’ files, exfiltrated more than 300GB of data over a two-month period and made beaconing connections to endpoints identified by OSINT as probable Cobalt Strike C2 servers.
Attack Details
In May an internal desktop was observed connecting to a rare external endpoint over the SSL protocol using a highly unusual port and the RClone client. These connections continued for several weeks and spiked at the same time as the device’s other malicious activity. It is likely that these connections reflected a potential point of infection.
The attacker then used the desktop and two other internal devices to perform network scanning and enumeration activity in order to discover other devices on the network it could infect. In total 856 unique IPs were scanned- largely over TCP, UDP and ICMP. Further directory replication service requests were also seen over DCE-RPC, suggesting an attempt to extract user credentials. One device was later seen accessing an unencrypted password file showing successful recon. The attacker then used the already compromised devices to infect other devices on the network by writing suspicious ‘.exe’ and ‘.dat’ files including ‘Bun.dat' and ‘Agent.exe’.
The compromised devices were then used by the attacker to download nearly 4GB of data from an internal server and to upload a similar amount to a suspicious IP address associated with a young domain. Over the following two months, the compromised devices went on to upload roughly 100GB of data to the same destination each week.
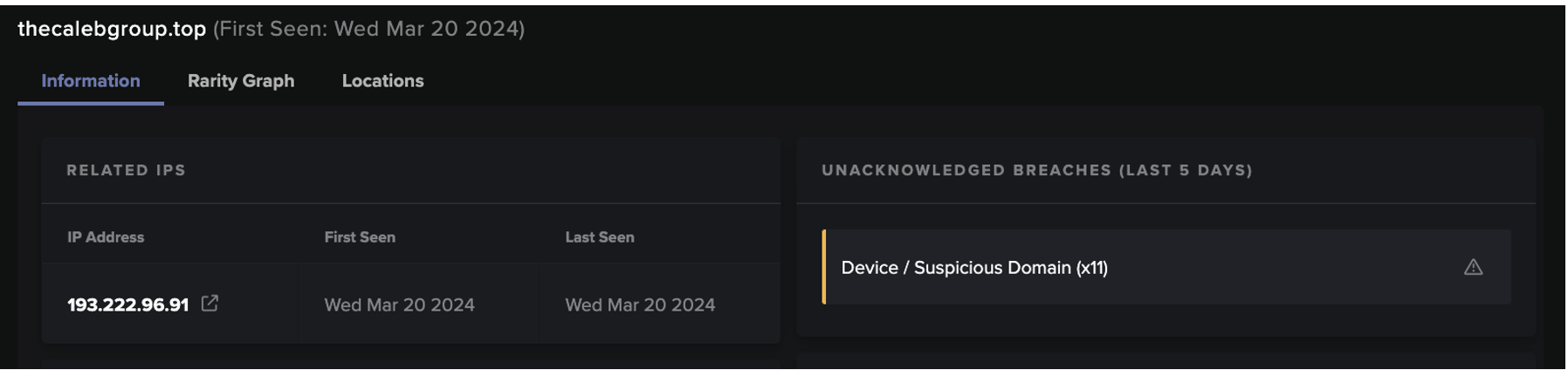
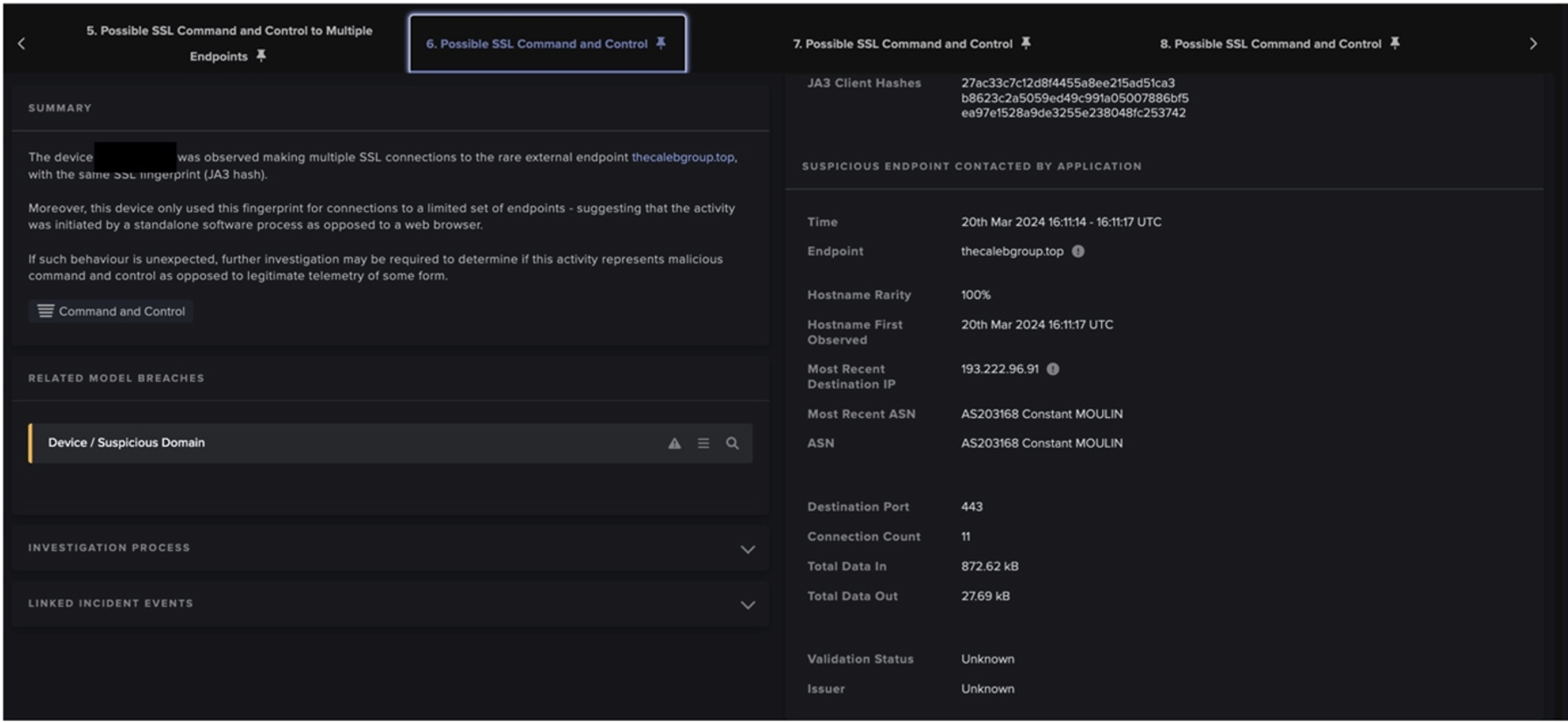
The attacker also used these devices to make beaconing connections to several rare and external endpoints. Some of these endpoints were created just before the beginning of the compromise and have all been identified by OSINT as probable Cobalt Strike command and control servers. During this beaconing an internal device was also observed making an extremely large number of writes of files that appeared to be ransom notes, these were appropriately named ‘YOURNETWORKDATAHASBEENCOMPROMISED.txt’.
Darktrace Coverage
How did this attack remain hidden from the company’s other tools? Neither the initial C2 IP Address, the follow-on Cobalt Strike C2 servers or the exfiltration server were associated with malicious activity in open-source reporting prior to this compromise. This meant they were likely omitted from expected blacklists and standard signature-based security. Furthermore, executable files written by the compromised devices included ‘anydesk.exe’ and ‘procdump64.exe’, both of which are legitimate tools commonly used by administrators. This demonstrates the use of living off the land tactics (LotL) which are typically hard to detect.
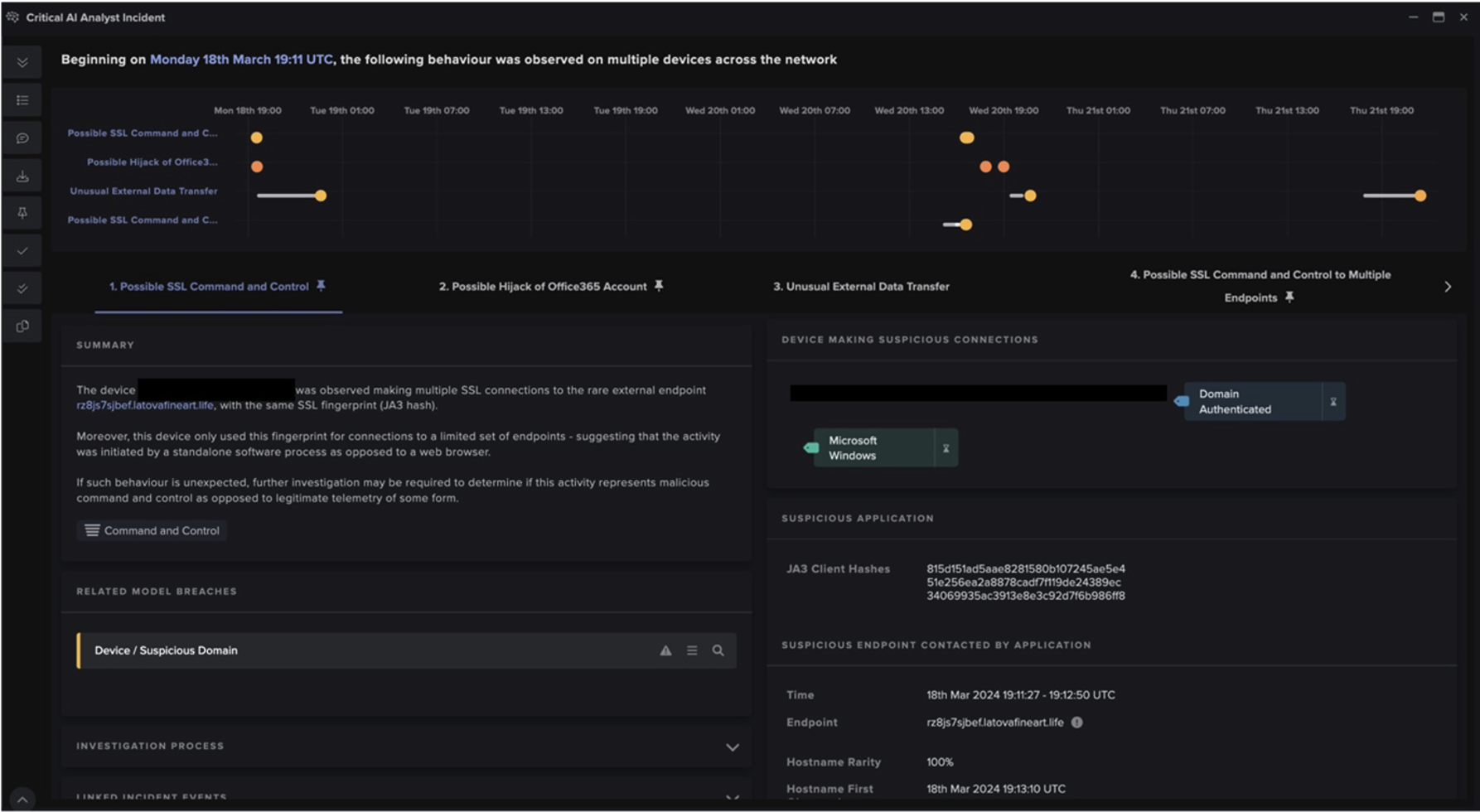
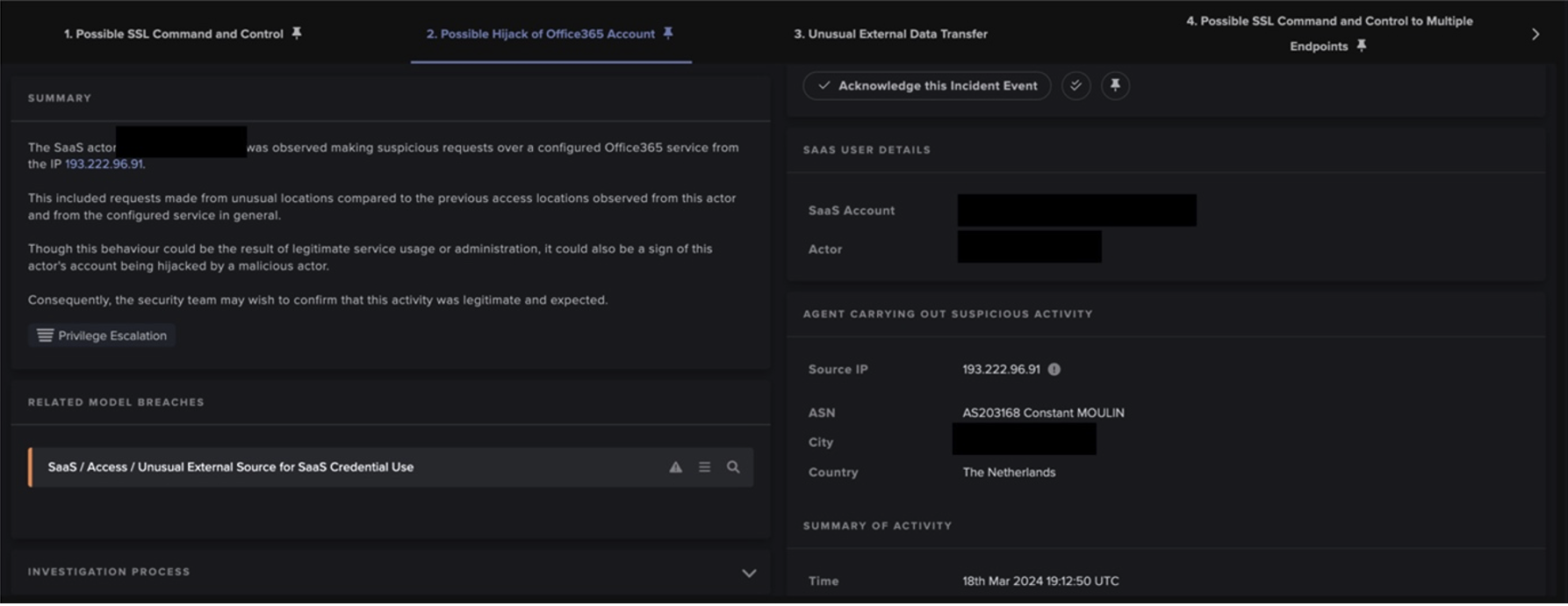
Given the attack’s novelty and LotL techniques, it is no surprise that Darktrace DETECT/Network identified anomalies in usual network behaviour. In particular, Cyber AI Analyst was a large highlight when it came to both Darktrace’s and the security team’s follow-up triage. AI Analyst collated different phases of the compromise such as the network scanning activity, the lateral movement activity over the DCE-RPC protocol, the data exfiltration, and the beaconing activity to the Cobalt Strike endpoints. This helped to map a clear timeline and progression of events along the kill chain.


On top of the DETECT product, Darktrace services had a large role to play in the aftermath. The customer subscribed to Darktrace’s Ask the Expert (ATE) service and only became fully aware of the compromise after submitting an ATE ticket requesting assistance investigating one of the related model breaches. Finally, RESPOND itself (although in human confirmation mode) was still able to be used to manually quarantine devices.
Schlussfolgerung
During this incident, the initial point of infection, data exfiltration endpoint, and Cobalt Strike C2 Servers were recently created and had no OSINT associating them with malicious activity. This demonstrates how ineffective traditional signature-based intrusion detection systems can be at detecting compromises and how effective Darktrace is at detecting novel campaigns and attacks. Despite this, detection is clearly not enough, especially as out-of-hours attacks increase in frequency and effectiveness. This customer had RESPOND in human confirmation mode which meant that the activity was acted upon and stopped slower than had it been set autonomously. If malicious data loss is to be stopped in full, companies need to reduce reliance on humans and embrace AI-based protection.
Thanks to Darktrace analyst Steve Robinson for his insights on the above threat investigation.
Appendices
Related AI Analyst Incidents
- Unusual Repeated Connections
- Suspicious DCE-RPC Activity
- Internal Download and External Upload
- Scanning of Multiple Devices
- Possible SSL Command and Control Activity to Multiple Endpoints
- Suspicious Remote WMI Activity
- Access of Probable Unencrypted Password File
- Extensive Suspicious DCE-RPC Activity
- Suspicious Remote Control Service Activity
Indicators of Compromise