REvil, auch bekannt als Sodinokibi, ist eine Ransomware-as-a-Service (RaaS)-Bande, die für einen der größten Ransomware-Angriffe der Geschichte verantwortlich ist. Am 14. Januar 2022 gab Russland bekannt, dass es 14 Mitglieder der kriminellen Bande verhaftet hat. Dieser Schritt erfolgte auf Ersuchen der US-Behörden, die gemeinsam mit internationalen Partnern hart gegen die Hacker vorgegangen sind. Im vergangenen Jahr wurden mehrere aufsehenerregende Angriffe der REvil-Gruppe zugeschrieben, darunter die Ransomware von JBS und die Vorfälle in der Lieferkette von Kaseya.
Die Verhaftungen sind sicherlich ein Sieg für die westlichen Strafverfolgungsbehörden und folgen auf die Ankündigung von Europol im November, dass in den vorangegangenen Monaten sieben REvil-Mitglieder verhaftet worden waren. Die Frage ist: Inwieweit werden diese Verhaftungen die Machenschaften der Kriminellen stören, und für wie lange?
Erste Hinweise von Sicherheitsforschern bei ReversingLabs deuten darauf hin, dass die REvil-Aktivität nicht beeinträchtigt wurde. Die Statistiken über REvil-Implantate sind zwei Wochen nach den russischen Verhaftungen unverändert und deuten eher auf einen leichten Anstieg hin.
Diese anhaltende Aktivität lässt auf eines von zwei Szenarien schließen:
- Die zahlreichen Verhaftungen betrafen nur die "Mittelsmänner" in der Hierarchie der kriminellen Organisation
- Das Ransomware-as-a-Service-Modell von REvil ist widerstandsfähig genug, um Störungen durch Strafverfolgungsbehörden zu überstehen
Beide Szenarien sind besorgniserregend für diejenigen, die Ransomware-Banden zum Opfer fallen könnten. Die Realität ist wahrscheinlich eine viel komplexere Mischung aus diesen und anderen Faktoren. Das Durchgreifen gegen Ransomware ist längst überfällig, aber der Kampf wird wahrscheinlich sehr langwierig sein. Die Strafverfolgungsbehörden müssen das Geschäftsmodell so weit unterbinden, dass es nicht mehr rentabel ist, im Ransomware-Geschäft mitzumischen. Dies wird wahrscheinlich Monate oder sogar Jahre in Anspruch nehmen.
Die Bekämpfung von Ransomware spielt sich auf der größten Bühne ab. Welchen Trost können Sicherheitsteams aus den jüngsten Ereignissen ziehen, wenn es überhaupt einen gibt?
Dem sich entwickelnden RaaS-Modell mit KI immer einen Schritt voraus
Ein gemeinsamer Bericht über Ransomware, der kürzlich vom FBI, CISA, NCSC, ACSC und der NSA veröffentlicht wurde, zeigt die wichtigsten Trends des vergangenen Jahres auf:
- RaaS hat sich zunehmend professionalisiert, Geschäftsmodelle und Prozesse sind inzwischen gut etabliert.
- Das Geschäftsmodell erschwert die Zuordnung, da es komplexe Netzwerke von Entwicklern, Partnern und Freiberuflern gibt.
- Ransomware-Gruppen tauschen Informationen über ihre Opfer untereinander aus, wodurch die Bedrohung für Unternehmen noch vielfältiger wird.
Zusammenfassend zeigt der Bericht, wie Ransomware-Banden immer anpassungsfähiger werden, wenn es darum geht, die Strafverfolgung zu umgehen und den Gewinn aus Lösegeldzahlungen zu maximieren. Mehrere Gruppen sind verschwunden oder haben sich zurückgezogen, nur um unter einem anderen Namen und mit einer leicht veränderten Strategie wieder aufzutauchen. Die Taktiken, Techniken und Verfahren (TTPs) unterscheiden sich von Opfer zu Opfer, was vor allem daran liegt, dass die Angriffe von verschiedenen Ransomware-Betreibern und angeschlossenen Unternehmen durchgeführt werden.
Dies ist beunruhigend für die Strafverfolgungsbehörden, die versuchen, gegen die Personen vorzugehen, die hinter diesen Angriffen stecken. Wenn eine RaaS-Gruppe wie REvil aus einem amorphen und sich ständig verändernden Netz von Partnern besteht, ist die Verhaftung einzelner Personen ein ständiges Hinterherlaufen und wird die Gruppe als Ganzes wahrscheinlich nicht zu Fall bringen.
Der gleiche Kampf spielt sich auch auf der Ebene einzelner Angriffskampagnen ab. Sicherheitstools, die sich auf die Merkmale früherer Bedrohungen konzentrieren, befinden sich ebenfalls in einer ständigen Aufholjagd: Bis ein einzelner Angriff erkannt, mit Fingerabdrücken versehen und für das nächste Mal gespeichert ist, haben sich die Angreifer und ihre Techniken bereits weiterentwickelt.
Aber es gibt noch eine andere Möglichkeit für Verteidiger, die zunehmend auf selbstlernende KI setzen, um Angreifern einen Schritt voraus zu sein. Indem sie Ihre digitale Umgebung erlernt und subtile Abweichungen identifiziert, die auf einen Angriff hindeuten, kann diese Technologie neuartige Angriffe bereits beim ersten Auftreten erkennen und darauf reagieren. Unten sehen Sie ein Beispiel dafür, wie die selbstlernende KI einen Angriff von REvil ohne Regeln oder Signaturen erkannt hat.
REvil Angriffe finden
Im Sommer 2021 startete ein REvil-Tochterunternehmen einen Angriff auf eine Organisation des Gesundheits- und Sozialwesens. Ein Sektor, in dem die Zahl der Cyberangriffe seit Beginn der weltweiten Pandemie stark zugenommen hat. Der Angriff wurde zwar von der KI ohne Verwendung von Regeln oder Signaturen erkannt, aber das Sicherheitsteam überwachte Darktrace zu diesem Zeitpunkt nicht. Da die autonome Reaktionentgegen aller Warnungen nicht live geschalten war, konnte der Angriff fortgesetzt werden.
Nachdem sich der Angreifer über den Laptop eines Remote-Mitarbeiters Zugang zum Netzwerk verschafft hatte, konnte er eine legitime Remote-Desktop-Verbindung (RDP) zu einem Jump-Server des Unternehmens missbrauchen, um weitere Anmeldedaten abzufangen.
Sobald der Angreifer über weitere Anmeldeinformationen verfügte, stellte er über RDP eine Verbindung zu mehreren internen Geräten her, darunter auch zu einem zweiten Jump-Server. Die Datenexfiltration begann von dem ursprünglich kompromittierten Server über den RDP-Port 3389.
Zwei Wochen später identifizierte der Angreifer die Kronjuwelen der Organisation, die auf einem dritten Server gespeichert waren, und versuchte, die Command-and-Control-Kommunikation (C2) zu initiieren. Der Server stellte eine Reihe ungewöhnlicher externer Verbindungen her, darunter Versuche, sich mit einer seltenen Domain zu verbinden, die dem Aktivitätsmuster ähnelte, das mit der früheren Kaseya-Ransomware-Kampagne von REvil verbunden war.
Darktrace for Endpoint, das auf Remote-Benutzergeräten ausgeführt wurde, sorgte für zusätzliche Transparenz und ermöglichte es dem Sicherheitsteam, das ursprünglich gefährdete Benutzergerät zu ermitteln. Wäre Antigena auf dem Endpunkt aktiv gewesen, hätte es eingegriffen, um diese ungewöhnliche Aktivität zu stoppen, indem es die spezifischen ungewöhnlichen Verbindungen blockiert hätte. Der Angriff wäre eingedemämmt worden, ohne den regulären Geschäftsbetrieb zu beeinträchtigen.
Verknüpfung der Punkte eines Low-and-Slow-Angriffs
Die Gesamtverweildauer der Angreifer betrug 22 Tage. Sie waren geduldig und führten ihre Aktionen in Schüben durch. Oftmals lagen Tage dazwischen. Dieses Verhaltensmuster ist für Ransomware-Angriffe nicht ungewöhnlich, insbesondere für solche, die das RaaS-Modell verwenden, bei dem jeder Schritt von verschiedenen Bandenmitgliedern oder verbundenen Unternehmen ausgeführt werden kann.
Der Darktrace Cyber AI Analyst war in der Lage, den gesamten Lebenszyklus des Angriffs über mehrere Wochen in Echtzeit zu verfolgen und die einzelnen Phasen des Angriffs zu einem kohärenten Sicherheitsvorfall zusammenzufügen.

Abbildung 1: Der Cyber AI Analyst zeigt die komplette Angriffskette auf
Neuer Name, gleiches Spiel
Bei diesem Angriff handelt es sich um einen weiteren Fall von Bedrohungsakteuren, die sehr gezielt vorgehen: Sie nutzen legitime Programme und Prozesse, die bereits in der Umgebung verwendet wurden, um bösartige Aktivitäten durchzuführen. Dies kann mit herkömmlichen Tools, die auf statischen Anwendungsfällen basieren und eine legitime RDP-Sitzung nicht von einer bösartigen unterscheiden können, sehr schwer zu erkennen sein.
Da cyberkriminelle Gruppen wie REvil weiterhin den Bemühungen der Strafverfolgungsbehörden trotzen, müssen Unternehmen mit KI-Technologie, die ihre Umgebung erlernt, aufrüsten. Autonomous Response wird bereits von Tausenden von Unternehmen in allen Bereichen der digitalen Infrastruktur eingesetzt - von E-Mail- und Cloud-Diensten bis hin zu Endgeräten, um Ransomware-Angriffe frühzeitig zu stoppen, bevor eine Verschlüsselung erfolgt.
Wir danken der Analystin Petal Beharry von Darktrace für ihren Einblick in die oben genannte Bedrohungslage.
Technische Einzelheiten
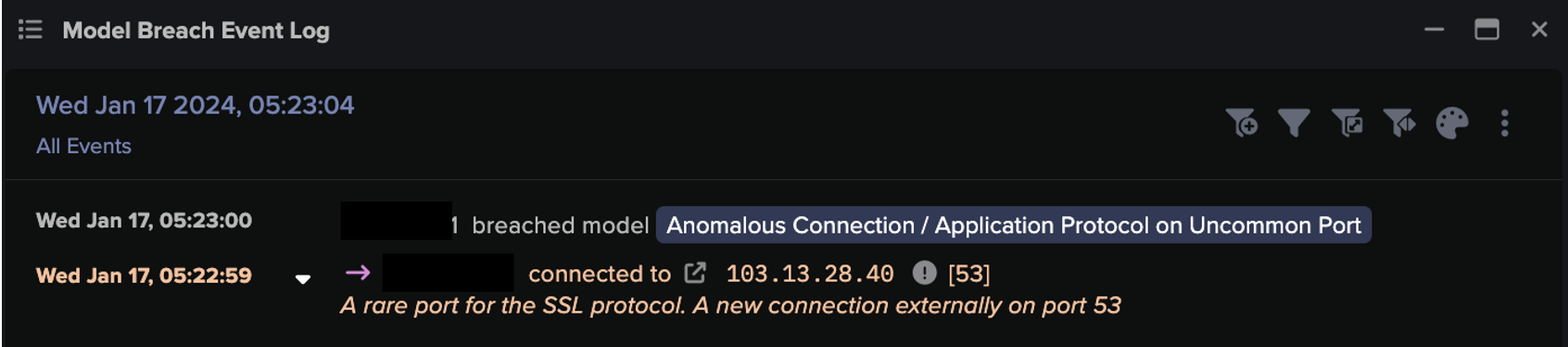
Darktrace Modell-Erkennungen:
- Device / RDP Scan
- Device / Bruteforce Activity
- Compliance / Outbound Remote Desktop
- Anomalous Connection / Upload via Remote Desktop
- Anomalous Connection / Download and Upload
- Anomalous Connection / Uncommon 1 GiB Outbound
- Anomalous Connection / Active Remote Desktop Tunnel
- Device / New or Uncommon SMB Named Pipe
- Device / Large Number of Connections to New Endpoints