AAA Washington kennt man hauptsächlich als Pannenservice, das Unternehmen ist aber auch in anderen Bereichen wie Versicherungen und Reisen tätig. Aus Sicherheitsperspektive haben wir zwei Prioritäten: Wir wollen richtig vorbereitet sind, um komplexe und weit verbreitete Bedrohungen wie Ransomware abzuwehren, und wir möchten die sensiblen Daten unserer Mitarbeiter und Mitglieder schützen.
Vor rund zwei Jahren waren wir an einem Scheideweg und mussten eine Entscheidung treffen. Unser Informationssicherheitsteam wusste, dass wir Lücken in der Echtzeitüberwachung hatten, insbesondere bei der 24/7-Response. Wir hatten zwar Tools und überprüften auch die Protokolle, aber es gab kein 24/7-Monitoring. Wenn also ein Angriff um 3 Uhr morgens stattgefunden hätte, hätten wir sicherlich nicht sofort Maßnahmen zur Eindämmung der Bedrohung ergreifen können.
Wir hatten also zwei Optionen. Das war unser Matrix-Moment, die Wahl zwischen der roten und der blauen Pille. Entweder waren wir bereit, eine lebensverändernde Wahrheit anzunehmen, oder wir würden den traditionelleren Weg einschlagen.
Für uns war die blaue Pille – und das, was uns viele damals empfahlen – die Beauftragung eines externen, rund um die Uhr arbeitenden Security Operations Center. Wir wussten, dass dies unser Problem lösen würde, aber auch mit vielen Nachteilen verbunden wäre, vor allem im Hinblick auf den Zeitaufwand: Man muss ein Service-Level-Agreement (SLA) vereinbaren, SNMP-Traps einrichten und Protokolle an das SOC übermitteln, das dann erst einmal all diese Protokolle durchforsten muss. Und dann muss sich das SOC neben AAA Washington ja auch um Hunderte anderer Kunden kümmern. Man muss eine Beziehung zu dem SOC-Mitarbeiter aufbauen, der aber anfangs die Nuancen der betreffenden Umgebung oder die Geschäftslogik nicht kennt …
Die Skepsis war daher verständlicherweise recht groß.
Und dann gab es da noch diese rote Pille. Für uns war das Darktrace mit seiner KI-Technologie, die sich eigenständig ein Bild von unserer Umgebung machen könnte und autonom auf sich entwickelnde Angriffe reagieren würde. Keine steile Lernkurve, kein ständiger Wartungsaufwand.
Wir mussten es einfach versuchen und testeten die Lösung zunächst in einer lokalen Konfiguration statt mit der Cloud. Das funktionierte reibungslos – wir bekamen die Box, schlossen sie an und schon waren wir startklar. Wenn uns das Produkt nicht gefallen hätte, hätten wir einfach den Stecker gezogen und es wieder zurückgeschickt.
Darktrace lieferte uns sofort neue Einblicke und schon in der ersten Woche erhielten wir den Warnhinweis, dass jede Nacht 1 GB Daten von unserer Backup-Appliance an ein Rechenzentrum an der Ostküste übertragen wurden. Wir dachten, wir wüssten, was in unserem digitalen Ökosystem vor sich geht, aber im Grunde hatten wir keine Ahnung. Darktrace lieferte uns genau die Erkenntnisse, die uns fehlten, und das zeigte uns, dass wir auf dem richtigen Weg waren.
Autonome Reaktion
Also volle Punktzahl bei Transparenz und Erkennung von Anomalien, aber was ist mit der Response-Funktionalität, wegen der wir überhaupt erst auf Darktrace gekommen waren? Wir waren gespannt, welche Maßnahmen Antigena empfehlen würde und wie präzise und tiefgreifend sie sein würden.
Da wir bei AAA Washington naturgemäß vorsichtig sind, richteten wir Antigena im Human Confirmation Mode ein. Das heißt, ein Mensch musste für die vorgeschlagenen Maßnahmen vorher grünes Licht geben. Es dauerte etwa zwei Wochen, bis sich die Technologie ein Bild von den Nuancen unserer digitalen Umgebung gemacht hatte, und schon nach kurzer Zeit konnten wir uns davon überzeugen, dass ihre Maßnahmen extrem präzise waren und sich nur minimal auf den regulären Betrieb auswirkten.
Antigena ergriff nie drastische Maßnahmen wie die Isolierung eines Geräts, sondern stoppte einfach nur die schädliche Aktivität. Die Technologie hat uns bei einigen der großen Angriffe, wie z. B. den SUNBURST-Attacken und zuletzt der Log4Shell-Sicherheitslücke, optimal geschützt.
Umstellung auf eine hybride Cloud-Strategie
In den zwei Jahren nach der Implementierung von Darktrace nahmen wir – wie viele andere auch – erhebliche Veränderungen an unserer digitalen Infrastruktur vor, darunter die Migration in die Cloud. Ich fragte mich, ob die Transparenz und der Schutz durch Darktrace darunter leiden würden.
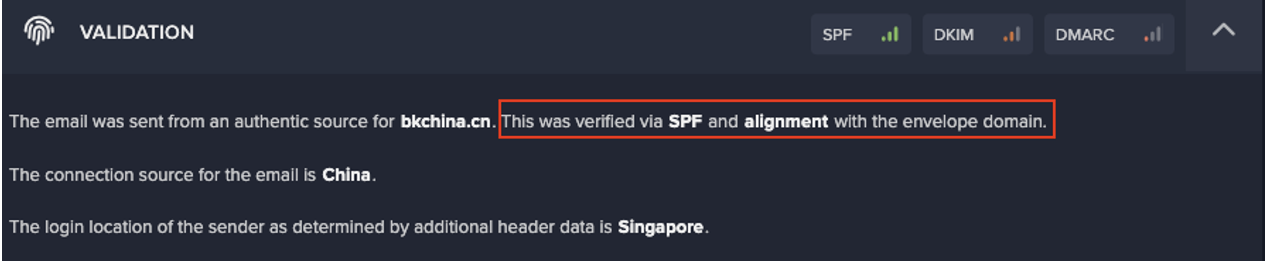
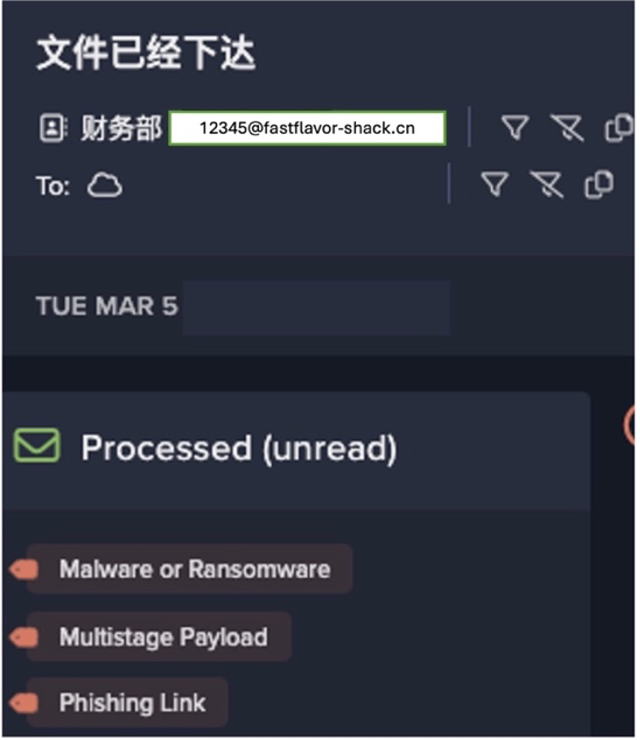
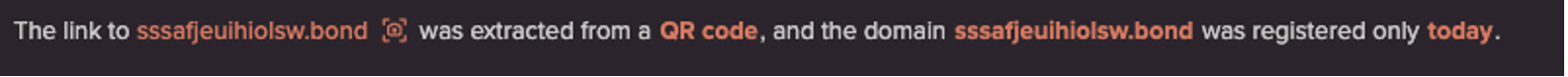
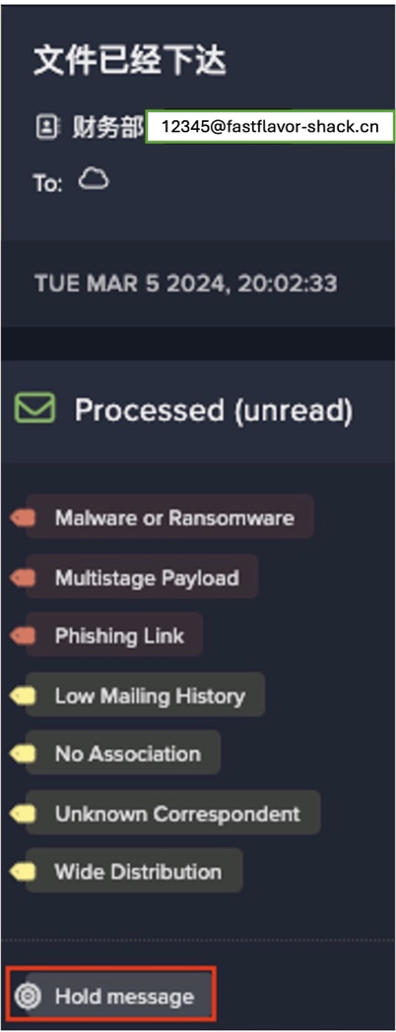
Das war aber kein Problem, weil Darktrace spezielle SaaS-Module für Microsoft 365 und andere Systeme anbietet. Die Technologie deckt schädliche Aktivitäten in unserer gesamten Microsoft 365 Produktsuite auf.
Wir werden zum Beispiel über ungewöhnliche E-Mail-Weiterleitungsregeln informiert, die auf eine Kontoübernahme hindeuten. Bei anderen Tools muss man erst sechs- bis achtmal klicken, bevor man diese Informationen findet. Und auch wenn die Informationen vorhanden sind, ist der Zugriff darauf komplex und wenig intuitiv. Darktrace ist in dieser Hinsicht so etwas wie der Heilige Gral, weil es alle wichtigen Einblicke in einem Sicherheitstool bündelt. Dank dieser zentralen, ganzheitlichen Sicht reduziert sich der Zeitaufwand für die Auswertung und somit für die Response.
Selbstlernende KI auf den Endgeräten
Als es zu der massiven Verlagerung der Arbeit ins Homeoffice kam, schützte Darktrace auch hier unsere Endgeräte durch Transparenz und Autonomous Response. Mit Netzwerkschutz allein würden Bedrohungen wie Ransomware schlichtweg unbemerkt bleiben. Dass solche Bedrohungen erkannt werden, bevor sie sich ausbreiten und weitere Geräte infizieren, war für uns entscheidend.
Damit stellte Darktrace wieder einmal seine Anpassungsfähigkeit unter Beweis – ein weiterer Grund, warum ich von einer langfristigem Zusammenarbeit mit Darktrace überzeugt bin: Jedes Mal, wenn ich denke, es könnte vielleicht auch ohne Darktrace gehen, werde ich von den aktuellen Entwicklungen eines Besseren belehrt.
Immer sicher unterwegs
Darktrace ermöglicht uns genau das, was wir uns gewünscht haben, nämlich eine 24/7-Response. Aber das ist längst alles: Die Technologie zeigt uns immer wieder, dass sie sich an Veränderungen unserer digitalen Infrastruktur anpassen kann, mit dem Unternehmen wächst und unsere Mitarbeiter jederzeit und überall schützt.
Darktrace liefert uns mit dem Threat Visualizer alle wichtigen Informationen in einer zentralen Ansicht. Mit der App erhalte ich Benachrichtigungen über Warnmeldungen mit hoher Priorität und die eigenständigen Maßnahmen von Darktrace, egal wo ich gerade bin. Und wenn es wirklich ernst wird, ist immer jemand da, der mir schnell hilft und sagt, was ich wissen muss.
Dass ich vor vielen Monaten die rote Pille gewählt habe, war eine der besten Entscheidungen, die ich als IT-Sicherheitsexperte getroffen habe. Egal welche Herausforderungen uns erwarten, ich bin zuversichtlich, dass wir sie mit Darktrace meistern werden.