A year and a half ago, ‘double extortion’ ransomware was being used by only one known threat actor. Now, over 16 ransomware groups actively utilize this tactic. So, what is it, and why has it become so popular?
What is double extortion ransomware?
The traditional story of ransomware was one of malicious code rapidly encrypting files with public-key RSA encryption, and then deleting those files if the victim did not pay the ransom.
However, after the infamous WannaCry and NotPetya ransomware campaigns over 2017, companies ramped up their cyber defense. More emphasis was placed on backups and restoration processes, so that even if files were destroyed, organizations had copies in place and could easily restore their data.
Yet in turn, cyber-criminals have also adapted their techniques. Now, rather than just encrypting files, double extortion ransomware exfiltrates the data first. This means that if the company refuses to pay up, information can be leaked online or sold to the highest bidder. Suddenly, all those backups and data recovery plans became worthless.
Maze ransomware and friends
In late 2019, Maze ransomware emerged as the first high-profile case of double extortion. Other strains soon followed, with the Sodinokibi attack — which crippled foreign exchange company Travelex — occurring on the final day of that year.
By mid-2020, hundreds of organizations were falling victim to double extortion attacks, various websites on the dark net were leaking company data, and the Ransomware-as-a-Service business was booming as developers sold and rented new types of malware.
Furthermore, cyber security regulations started being weaponized by cyber-criminals who could leverage the threat of having to pay a hefty compliance fine (CCPA, GDPR, NYSDFS regulations) to encourage their victims to keep quiet by offering them a ransom smaller than the penalty fee.
There were 1,200 double extortion ransomware incidents in 2020, across 63 countries, with over 60% of these aimed at the US and the UK.
Despite new legislation being written regularly to try and mitigate these attacks, they aren’t slowing down. According to a recent study by RUSI, there were 1,200 double extortion ransomware incidents in 2020 alone, across 63 different countries. 60% of these were aimed at organizations headquartered in the US, and the UK suffered the second highest number of breaches.
Last month, the cyber-criminal gang known as REvil released details about Apple’s new Macbook Pro on their site ‘Happy Blog’, threatening to release more blueprints and demanding a ransom of $50 million. And last week, Colonial Pipeline purportedly paid $5 million in bitcoin to recover from a devastating OT ransomware attack.
Anatomy of a double extortion ransomware attack
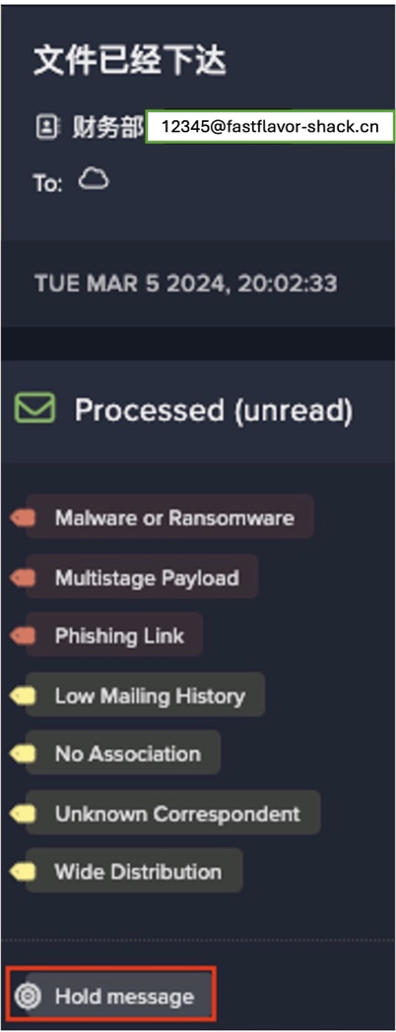
Darktrace has detected a huge upsurge in double extortion ransomware threats in the last year, most recently at an energy company based in Canada. The hackers had clearly done their homework, tailoring the attack to the company and moving quickly and stealthily once inside. Below is a timeline of this real-world incident, which was mostly carried out in the space of 24 hours.

Abbildung 1: Die Timeline des Angriffs
Darktrace detected every stage of the intrusion and notified the security team with high-priority alerts. If Darktrace Antigena had been active in the environment, the compromised server would have been isolated as soon as it began to behave anomalously, preventing the infection from spreading.
Encryption and exfiltration
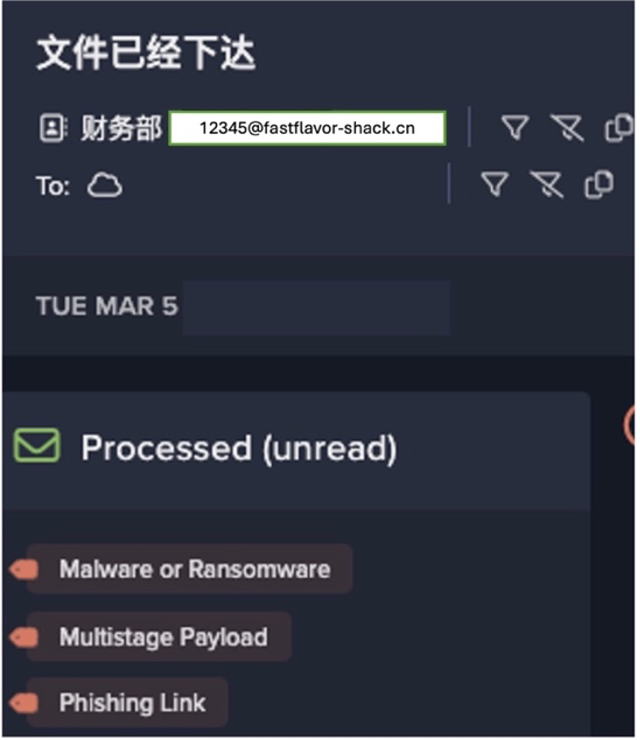
The initial infection vector is not known, but the admin account was compromised most likely from a phishing link or a vulnerability exploit. This is indicative of a trend away from the widespread ‘spray and pray’ ransomware campaigns of the last decade, towards a more targeted approach.
Cyber AI identified an internal server engaging in unusual network scanning and attempted lateral movement using the Remote Desktop Protocol (RDP). Compromised admin credentials were used to spread rapidly from the server to another internal device, ‘serverps’.
The device ‘serverps’ initiated an outbound connection to TeamViewer, a legitimate file storage service, which was active for nearly 21 hours. This connection was used for remote control of the device and to facilitate the further stages of attack. Although TeamViewer was not in wide operation in the company’s digital environment, it was not blocked by any of the legacy defenses.
The device then connected to an internal file server and downloaded 1.95 TB of data, and uploaded the same volume of data to pcloud[.]com. This exfiltration took place during work hours to blend in with regular admin activity.
The device was also seen downloading Rclone software – an open source tool, which was likely applied to sync data automatically to the legitimate file storage service pCloud.
The compromised admin credential allowed the threat actor to move laterally during this time. Following the completion of the data exfiltration, the device ‘serverps’ finally began encrypting files on 12 devices with the extension *.06d79000.
As with the majority of ransomware incidents, the encryption happened outside of office hours – overnight in local time – to minimize the chance of the security team responding quickly.
AI-powered investigation
Cyber AI Analyst reported on four incidents related to the attack, highlighting the suspicious behavior to the security team and providing a report on the affected devices for immediate remediation. Such concise reporting allowed the security team to quickly identify the scope of the infection and respond accordingly.

Figure 2: Cyber AI Analyst incident tray for a week
Cyber AI Analyst investigates on demand
Following further analysis on March 13, the security team employed Cyber AI Analyst to conduct on-demand investigations into the compromised admin credential in Microsoft 365, as well as another device which was identified as a potential threat.
Cyber AI Analyst created an incident for this other device, which resulted in the identification of unusual port scanning during the time period of infection. The device was promptly removed from the network.

Figure 3: Cyber AI Analyst incident for a compromised device, detailing an unusual internal download
Double trouble
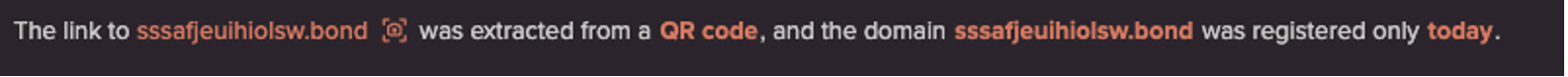
The use of legitimate tools and ‘Living off the Land’ techniques (using RDP and a compromised admin credential) allowed the threat actors to carry out the bulk of the attack in less than 24 hours. By exploiting TeamViewer as a legitimate file storage solution for the data exfiltration, as opposed to relying on a known ‘bad’ or recently registered domain, the hackers easily circumvented all the existing signature-based defenses.
If Darktrace had not detected this intrusion and immediately alerted the security team, the attack could have resulted not only in a ‘denial of business’ with employees locked out of their files, but also in sensitive data loss. The AI went a step further in saving the team vital time with automatic investigation and on-demand reporting.
There is so much more to lose from double extortion ransomware. Exfiltration provides another layer of risk, leading to compromised intellectual property, reputational damage, and compliance fines. Once a threat group has your data, they might easily ask for more payments down the line. It is important therefore to defend against these attacks before they happen, proactively implementing cyber security measures that can detect and autonomously respond to threats as soon as they emerge.
Learn more about double extortion ransomware.
Darktrace Modell-Erkennungen:
- Device / Suspicious Network Scan Activity
- Device / RDP Scan
- Device / Network Scan
- Anomalous Connection / Unusual Admin SMB Session
- Anomalous Connection / Unusual Admin RDP Session
- Device / Multiple Lateral Movement Model Breaches
- User / New Admin Credentials on Client
- Anomalous Connection / Uncommon 1 GiB Outbound
- Anomalous Connection / Low and Slow Exfiltration
- Device / Anomalous SMB Followed By Multiple Model
- Anomalous Connection / Download and Upload
- Anomalous Connection / Suspicious Activity On High Risk Device
- Anomalous File / Internal::Additional Extension Appended to SMB File
- Compromise / Ransomware::Suspicious SMB Activity
- Anomalous Connection / Sustained MIME Type Conversion
- Device / Anomalous RDP Followed By Multiple Model Breaches
- Anomalous Connection / Suspicious Read Write Ratio
- Device / Large Number of Model Breaches