Im Vorfeld der Präsidentschaftswahlen 2020 in den USA versuchten Microsoft und seine Partner, die tückische Trickbot-Malware aus dem Verkehr zu ziehen und eine Wahlmanipulation zu verhindern. Diese Bemühungen waren zu einem gewissen Grad erfolgreich: 94% der Infrastruktur wurden zerschlagen und Trickbot konnte Ende 2020 massiv zurückgedrängt werden.
Malware ist jedoch nicht so leicht tot zu kriegen. Wir haben bereits darüber gesprochen, dass die Festnahmen nach den breit angelegten REvil-Angriffen im Jahr 2021 dem Ransomware-as-a-Service-Geschäft der Cybergang kaum geschadet haben und dass die Ryuk-Ransomware in neue Hände übergegangen ist, nachdem ihre Entwickler sie aufgegeben hatten.
Das Comeback von Trickbot nahm noch viel größere Dimensionen an. Im Juni 2021 erkannte Darktrace einen Trickbot-Angriff in einer Kundenumgebung. Dabei war die Malware alles andere als ein veraltetes, ineffizientes Schadprogramm. Im Gegenteil, sie war auf einmal die weltweit dominierende Malware.
Nur weil der Kunde in letzter Minute die Autonomous Response von Darktrace aktiviert hatte, konnte verhindert werden, dass der Ransomware-Angriff zum Erfolg führte. Da die Autonomous Response in jeder Phase eines Angriffs Maßnahmen ergreifen kann, konnte sie Trickbot stoppen und die Ausführung von Ransomware verhindern, obwohl sich die Malware bereits in der digitalen Umgebung eingenistet hatte.
Trickbot nistet sich ein
Der Angriff fand bei einer öffentlichen Verwaltung in der EMEA-Region statt. Bereits vor der Implementierung von Darktrace war ein einzelner interner Domain-Controller von Trickbot kompromittiert worden. Der Angreifer wartete dann erst einmal ab. Als die Malware begann, aktiv zu werden, war die Darktrace KI schon implementiert. Obwohl die Umgebung bereits kompromittiert war, konnte die KI zwischen unschädlicher und schädlicher Aktivität unterscheiden und die Bedrohung sofort erkennen. Die Autonomous Response war allerdings so konfiguriert, dass sie ohne Freigabe durch das Sicherheitsteam keine Maßnahmen ergriff.
Darktrace erkannte, dass der kompromittierte Domain-Controller über SMB eine schädliche DLL-Datei – sehr wahrscheinlich Trickbot selbst – an rund 280 Geräte in der Verwaltung schickte und diese dann mit Windows Management Instrumentation (WMI) konfigurierte und ausführte. Obwohl es sich bei Trickbot um eine bekannte und berüchtigte Malware handelt, wurden Tools, die auf historischen Bedrohungsdaten basieren, in dieser Phase nicht auf die Gefahr aufmerksam.

Wie die Angreifer Trickbot zu neuem Leben erweckten
Aufgrund seiner modularen Beschaffenheit ist Trickbot die perfekte Ausgangsbasis für eine ganze Reihe krimineller Aktivitäten. Die Malware selbst ist dadurch sehr anpassungsfähig und nur schwer abzuwehren. Durch die von Microsoft koordinierten Maßnahmen konnten die bekannten IP-Adressen diverser Command & Control (C2)-Server für Trickbot stillgelegt und Trickbot-Betreiber am Kauf oder der Miete neuer Adressen gehindert werden. Es dauert aber nicht lange und die Trickbot-Infrastruktur war wieder aufgebaut. Im Mai und Juni 2021 wurde die Malware in einem globalen Bedrohungsindex als dominierend gelistet.
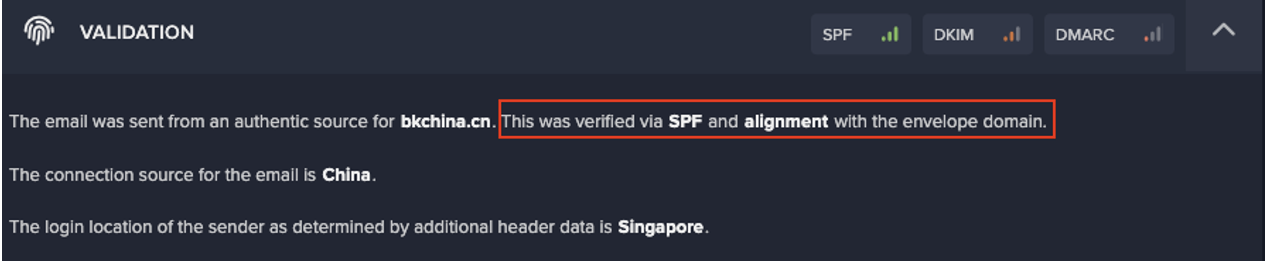
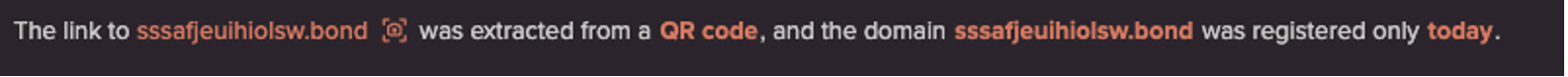
Dieser Angriff war der beste Beweis für die Fähigkeit von Trickbot, sich weiterzuentwickeln und vorhandene OSINT zu umgehen. Darktrace stellte fest, dass 160 der erkannten 280 kompromittierten Geräte anfingen, eine Verbindung zu mehreren neuen C2-Endgeräten aufzubauen. Keines davon wurde auf Basis von OSINT mit schädlicher Aktivität in Verbindung gebracht. Darktrace dagegen stufte das Verhalten angesichts der bisherigen Verhaltensmuster als sehr ungewöhnlich ein und informierte das Sicherheitsteam mit einer Proactive Threat Notification (PTN) über diesen potenziell schwerwiegenden Vorfall.
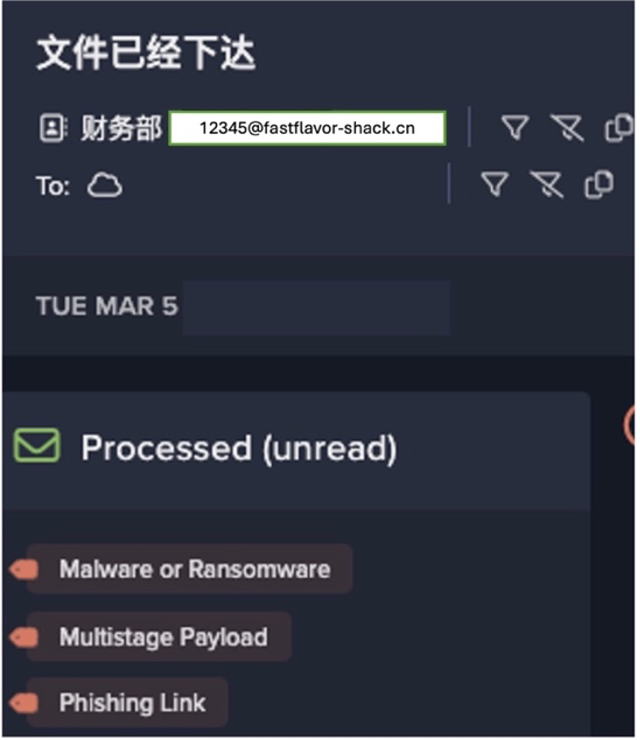
Die Angreifer ließen sich über einen Monat Zeit, bis die kompromittierten Geräte getarnte ausführbare Dateien herunterluden und anormale Scanaktivitäten ausführten. Diese Dateien waren mit hoher Wahrscheinlichkeit Ryuk-Ransomware-Payloads. Durch den großen Abstand zwischen den einzelnen Angriffsphasen machten es die Bedrohungsakteure den menschlichen Teams schwer, die Zusammenhänge und somit das ganze Ausmaß der Bedrohung zu erkennen.
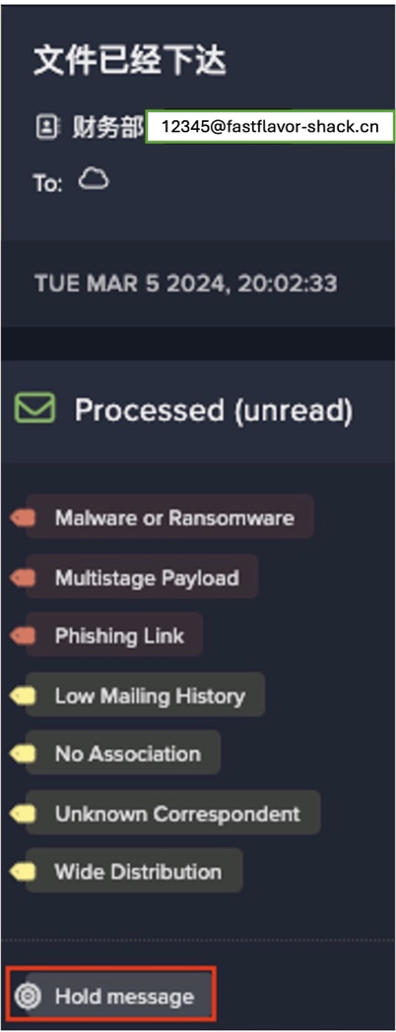
Der Darktrace Cyber AI Analyst, der Bedrohungen in allen digitalen Umgebungen untersucht und bewertet, konnte diese isolierten Ereignisse jedoch zu einem Gesamtnarrativ des Angriffs zusammensetzen und eine weitere PTN herausgeben. Aufgrund der Dringlichkeit der Situation nahm der Kunde den „Ask the Expert“-Service (ATE) von Darktrace in Anspruch, um Unterstützung bei der Abwehr der Bedrohung zu erhalten.

Abbildung 2: Cyber AI Analyst untersucht verdächtige ausführbare Dateien, die an mehrere interne Geräte geschickt wurden.
Autonomous Response stoppt Angriff in einer späten Phase
Nachdem das Team das Ausmaß der akuten Bedrohung verstanden hatte, aktivierte es Autonomous Response mit eigenständigen Maßnahmen zur Eindämmung der Bedrohung. Wäre Autonomous Response von Anfang an aktiviert gewesen, wäre dieser Angriff in den Anfangsphasen gestoppt worden, als er sich noch auf einen einzelnen kompromittierten Domain-Controller beschränkte. Entscheidend ist jedoch, dass die Autonomous Response in jeder Phase einer Ransomware-Attacke eingreifen kann.
Selbst in dieser späten Phase war die Technologie in der Lage, den Angreifern Einhalt zu gebieten und zu verhindern, dass Ryuk im Netzwerk ausgeführt wird. Die KI blockierte binnen Sekunden eine Kette schädlicher Aktivitäten, unter anderem SMB-Enumeration, Netzwerkscans und verdächtige ausgehende Verbindungen, und stoppte dadurch den Angriff. Der Geschäftsbetrieb lief dabei ganz normal weiter.
Da die C2-Kommunikation und die laterale Bewegung unterbrochen wurden, konnten die Angreifer Ryuk und somit auch den Angriff nicht ausführen. Es ist sehr wahrscheinlich, dass die Last-Minute-Aktivierung der Autonomous Response eine umfangreiche Verschlüsselung und möglicherweise auch Exfiltration von Daten verhinderte. So blieben dem Unternehmen die hohen Kosten erspart, die mit einem erfolgreichen Ransomware-Angriff verbunden sind, selbst wenn ein Lösegeld gezahlt wurde.
Autonomous Response aktivieren, bevor es zu spät ist
Obwohl Darktrace erst aktiviert wurde, nachdem sich der Angreifer eingenistet hatte, konnte die KI die schädliche Aktivität vom normalen Geschäftsbetrieb unterscheiden und die Bedrohung ohne Störungen stoppen. Sollte es erneut zu einem Angriff kommen, ist das Unternehmen vorbereitet: Die Autonomous Response befindet sich von vornherein im autonomen Modus und kann beim ersten Hinweis auf eine sich entwickelnde Bedrohung effektiv und minimalinvasiv eingreifen.
Der Weg zu vollautonomer Sicherheit setzt voraus, dass die Unternehmen Vertrauen in die Präzision und die Entscheidungen der KI aufbauen. Dieser Weg gestaltet sich bei jedem Unternehmen anders, aber keines sollte auf die harte Tour lernen müssen, wie wichtig eine eigenständig agierende Sicherheitslösung ist.
Vielen Dank an unseren Darktrace Analysten Sam Lister für die Einblicke in diesen Bedrohungsvorfall.